In the next installment of our series on conversations Early Adopter Research’s Dan Woods had about cybersecurity at RSA 2019, this podcast is an interview he had with Illumio’s Andrew Rubin, the company’s co-founder and CEO, and PJ Kirner, the company’s co-founder and CTO. Woods asked about his three key cybersecurity questions for the year, as well as having his guests explain Illumio’s fit in the cybersecurity landscape. The interview included:
* 3:00 – The need for segmentation in cybersecurity
* 10:00 – What CISOs should do with zero trust
* 17:30 – Managing risk in cybersecurity
* 24:20 – Improving operational discipline in cybersecurity
* 35:00 – Managing cyber insurance
Listen below:
Q&A
Woods: What Illumio does is create a system that has a white list where you can define every network path so that what you’re defining is all of the approved ways that traffic can flow. You have what I consider is a domain specific language where you describe how you want that to look at and then that domain specific language translates that into the instructions that are used for the network configuration. From there, you declare policies about how you want that network to be configured or how you want it to be changed and essentially you’ve got underneath there a semantically tagged graph and you can then modify and make rules about that graph with policies of other. And then you can handle a very complex network configuration in an abstract way. Is that a fair way to describe what Illumio does?
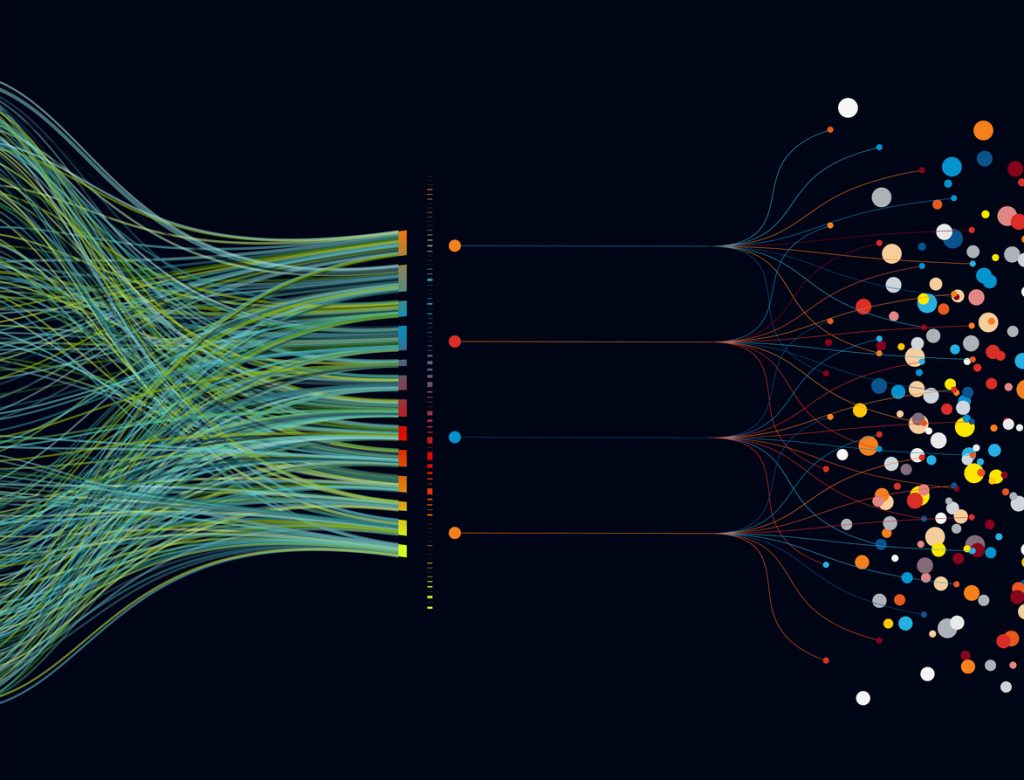
Rubin: That is a fair way to describe it. I want to add a word to your description that I know for us and our customers is very important which is, although you’re right that network and infrastructure and certainly traffic and flows are all very important and relevant, the word application is really at the center of the universe. Our customers are not thinking about just flows and networks and connections, they’re thinking about the application context and the application story. When we say should two things talk to each other, it’s certainly relevant to talk about the IP addresses and the flows but what the customer is really asking is should this piece of an application talk to this piece of an application or should this environment called development be talking to this environment core production? The only other color that I would like to add is it’s important to talk about outcomes, much more so than just technology. There is a reason why customers five years ago weren’t thinking about or even using the word network segmentation or micro-segmentation. And it’s because the outcome wasn’t necessarily a priority. But when you think about it, in today’s world there are two consistent and pervasive problems that everybody seems to want to solve. The first is a very often complete and sometimes utter lack of understanding of what’s actually running inside of the datacenter, cloud compute environment. Organizations will consistently tell us that they’re missing information about certain systems, certain connections, and how things are talking to each other. When we built Illumio, the first problem that we set out to solve was not segmentation, it was simply building the map, visualizing the graph that you mentioned so that for the first time customers could have an accurate and complete understanding of all their workloads, how all these things are connected and talking to each other and probably most importantly that application story laying on top of the infrastructure story and being presented as one.
I’ve come to understand in talking to different people about Illumio is that there are two use cases when you first start to use the product. The first use case is when you have an existing network and then you try to map and tag it and when you do that you find some surprises. The second use case is when you are creating and putting in this Illumio map and these Illumio tags as part of an automatically created infrastructure in the cloud or an automatically provisioned network on premise.
Kirner: You’re absolutely right. There’s those two motions. One we call the brownfield motion and it is infrastructure and applications that are already in play. That map is critical to the understanding and the ‘aha’ moments that our customers have and then applying segmentation there. As well as, I’ll call it greenfield which is a new application coming online maybe with a dev ops kind of style and being able to bake security in as early in the lifecycle as possible.
That is a semantically tagged graph so that you can now start setting rules according to the semantic tagging, not a micro level. That has a tremendous effect on the simplicity of the problem.
Kirner: You’re absolutely right there, so for example, we had a customer who had a datacenter and had some firewalls to meet their segmentation goals and they had 15,000 firewall rules necessary to accomplish that. They moved to a new datacenter architecture and used us instead, Illumio instead, and they were able to accomplish those same goals with 40 Illumio policies.
Rubin: I also want to add as one of the underpinnings of the whole conversation which is the world is not binary and it certainly is not one flavor. One of the things that from the very beginning, PJ and I believed that the world is heterogenous and will remain heterogenous. We also believe very deeply that neither of us would have any idea what the world would look like tomorrow. The assumption that we made was that whether it’s building a map or driving segmentation policy, you really have to be able do it in a way that’s decoupled or agnostic from a particular platform or infrastructure model. Whether it’s bare metal VMs or obviously containers nowadays, the world is mixed and mixed up and it’s going to probably remain that way in some way, shape or form forever. We really wanted to be able to deliver Illumio in a way that wasn’t dependent on one of those assumptions holding true.
Another way of thinking about this is that you have picked up on what makes SQL so great which is creating a declarative language that can be implementation independent. So you can describe the network state and then you switch out a Cisco router for a Wave router and you can still just reapply the programming to that router based on the declarative language.
Kirner: Fundamentally, what our system is, is a giant graph engine, that declarative language on top of a graph engine. And more importantly, it’s a dynamic system because the world is not getting slower, it’s getting faster, more and more compute that’s spinning up with containers and public cloud and this thing needs to be able to recompute on the fly to continue to apply those kind of principles uniformly. And even in the face of change.
Let’s move on to the three questions. The first one is about zero trust. How can a CISO understand and make zero trust, which is a buzz word that has lost its meaning, but there’s something important underneath it which is the idea that the perimeter is no longer as important and it can’t really work to create a zone of safety. Inside the perimeter you need to be able to have the assumption that everything inside there might be compromised and how do you deal with that fact? When I’ve talked to people about zero trust it like it boils down to the idea of creating better authentication, creating a way of possibly having a cloud gateway, having the ability to look for threats and also having better device management. If you did all those things, that’s sort of like a reasonable step toward zero trust. But can’t buy zero trust off of a shelf, so what would you advise CISOs to do to rightfully embrace the good ideas in zero trust but also to do something practical that’s going to help them?
Kirner: From my point of view, one of the critical concepts of zero trust that came before Google, was the concept of least privilege — it’s been around for 20-plus years. Least privilege applies to users as your point of authentication comes in — users should have a minimal level of access to their systems. What happened with the perimeter is we had this perimeter and we lost the idea of least privilege. That’s what when you think about inside the perimeter, you have access to everything. But that’s changing and so people are again applying that principle of least privilege to users.
Rubin: Zero trust may start as a concept and it never gets all the way to a fully prescriptive architecture because that implies every organization would buy three controls and say, “We’re done.” I think what it is, is it’s a framework and it’s probably a framework and some architecture mixed in, it’s a set of security controls and there’s probably over time going to evolve to be a set of core controls that will be non-negotiable. And then remember that every organization is different, every organization has slight differences, sometimes major differences in their infrastructure model or their application model. The outcome of zero trust is exactly that, it’s a non-prescriptive but very real security framework, security architecture but how you get there and the specific controls and obviously the specific vendors that you choose to get there with, I think that that’s something that will shift and over time even organization by organization, it will adapt.
Kirner: It’s a journey and again, you have to be pragmatic about that.
Zero trust has always been something in which the segmentation around a particular user might change based on what I’m trying to do. Is it possible for Illumio to support that configuration where I’m going in and I’m just accessing email and then the Illumio policy surrounding me might be X rule? But then when I come in later and I want to access the trunk source code tree, then somehow I get a different segmentation.
Kirner: Absolutely. That model whether it be where you’re coming from, your device posture, or behavior analysis, all those things are part of how you would assess the access that is allowed at that point in time.
Can those policies be set in real time by Illumio?
Kirner: It can do all that detection but the Illumio policy model is incredibly dynamic and the policy compute engine is incredibly dynamic so all that can change in real time, absolutely. It is intended to be dynamic and rapidly change as the situation changes.
The cybersecurity world has new products for new uses every year and it seems like the portfolio in place at most companies never gets smaller. That’s reasonable because the attack surface has gotten bigger, you now have many more types of attack surface that you need to protect and so it goes to reason that you should also have more ways of protecting that. But it also seems reasonable that as we’ve gotten smarter and as we’ve understood the problem better, shouldn’t we be able to prune that portfolio and either prune the number of vendors we have, the complexity of the process of doing this or having new capabilities replace and make obsolete older capabilities?
Rubin: You’re right that there’s been an explosion in just about every measurable sort of metric around cyber. Amount of capital invested, number of vendors, the problems we’re trying to solve. The more interesting point underneath it though we should be careful not to conflate the attack surface getting bigger with the problem becoming more complex and therefore needing more vendors or more solutions or more products to solve it. The problem can become bigger but that doesn’t necessarily mean that you need more tools to solve it.
But so far it has.
Rubin: It has so far because that’s been our strategy and I guess what I would say is when I spend time talking to CIOs, certainly CISOs and customers in general, you hear them talking about now they’re no longer interested in having the conversation about technology for technology’s sake or tools that solve a problem. What they want to do is they want to start the conversation by understanding the risk. And when they look at the risk and they say, “Look, this is the risk that I’m trying to manage or shrink or control,” then all of a sudden the vendor the product, the solution is mapped against a risk and I think that that’s been missing in cyber for a long time. At the end of the day, the two things that we’re all certain of is, one, we can’t reduce risk to zero. It doesn’t matter how many products you buy, how much money you spend, how many people you hire, you will not build something that will be totally safe 100%. You’re also going to see customers do what you described in the question which is they’re going to start to look at the pruning. They’re going to start to ask, “If I took this tool away, how much more risk am I really going to have as a result of it?” And I don’t think it’s something that happens overnight, it’s not a light switch but I think after years of growth in number of tools, number of solutions, number of vendors, you’re right that there is this shift in the conversation where customers are starting to say, “I have this risk, it is a business risk like any other, I have to find ways to manage it, reduce it and control it and I’m going to look at the things that I buy and make sure that there’s alignment.”
What’s interesting about what you said is that I do believe that people are starting to understand that there are incompatibilities between product groups. I would suspect that you and your customers are on the low-end of adopting deception technology because once you have a really tightly defined network, deception becomes less important. If you have an environment in which you, because of your business needs, have to have a wide-open network, that would make more sense to have deception technology.
Kirner: The first challenge is there’s overlapping products, things that actually do solve effectively the same problem. You can have A or you can have B and somebody might have A and B in there and if you remove one of them, you meet the same kind of risk criteria. People have to start looking at that overlap and if you had a highly segmented network and you applied deception, the efficacy of deception in a highly segmented network might be very well. But if you applied deception in an unsegmented network, the efficacy could be high.
There are a few companies out there that were born in the cloud and don’t have a perimeter. I could imagine that in such a case, you might be able to get away without having a firewall.
Rubin: The reality is that most of the world still does run in brownfield so yes, if you are a brand new company and you’re setting up brand new infrastructures to support a brand new business and business model, then obviously that puts you in an unbelievably advantageous place in terms of not having the legacy or the existing plant to deal with. But the reality is that most organizations live in this bifurcated world, mostly old, trying to get to more new. We don’t really think of it in terms of you wouldn’t have to have this or you wouldn’t have to have that, we look at it as look at the environment, look at the risk in the environment and then find the proper controls. All products for the most part have some ability to provide either information data or visibility and then you come back to the question of that is generically true but how much value am I getting out of that visibility and do I need it versus do I want it? And at some point, there is certainly a conversation around value that a product or a solution brings. Don’t forget that on the other side of the balance sheet is the cost of not just purchasing it but operationalizing it, integrating it and maintaining it.
Right now cybersecurity is dealing with the cloud in a variety of ways. One way is that cybersecurity solutions are migrating to the cloud and being implemented there, although the bulk of the spending is for on premise solutions. But the second thing is how do you move to the cloud and protect the assets in the cloud in this whole different environment? How do you manage this transition without creating another layer of fiendish complexity as well?
Kirner: You make a good point about the migration to cloud. One thing that you get, whether you’re going to SaaS where you have a large SaaS provider that’s providing security for your data or whether you’re going to IaaS and adopting an AWS model as infrastructure as a service, what you get is rather than having artisan security, you get security that has been built at scale. I love the one Amazon practice of they don’t let any disc drives out of their datacenters at all. Every single one goes through the chipper and there’s no other option. In terms of some of the security offerings, we at Illumio provide a SaaS offering and an on prem offering. The vendors do need to provide customer’s choice, being able to provide a security control that works on prem, works in private cloud, works in public cloud, that’s kind of the thing that as people adopt these things and as we said before it’s a hybrid environment, you have to have security tools that work through that.
At the highest level of security, you probably want to have an independent way of confirming that there are no problems?
Rubin: Yes, it’s really interesting. When you buy a house or an apartment or you rent a house or an apartment in a neighborhood, yourely on the neighborhood to provide a certain level of base protection. There’s a police department, they are presumably going around and making sure that generally the streets are safe. But the reality is that what goes on behind your front door whether you choose to put an alarm on, maybe you put cameras up if you really want to have great security in your house or your apartment, those are all decisions that you have to make for yourself. And in a lot of ways, the two are neither complementary nor in conflict in that the decisions that you make about what you do within your own four walls, you don’t necessarily integrate those, and have interoperability with what’s happening on the streets. But at the same time, it’s hard to argue that if you choose to overinvest or heavily invest inside of your own four walls that you don’t have a safer house. That’s a good metaphor for migrating to the cloud. They’re going to benefit if those basic security controls or investments have been made on their behalf, something that back home they would have done themselves, it’s possible somebody is now doing it for them but there still is a whole set of security controls that they have to do decide on their own whether or not they want to invest in.
I have three other questions we go through really quickly. One is about ops discipline. It seems like that everybody should try to improve constantly their operational discipline, better configuration, patch management, asset inventory, automation, all of that pays huge dividends. But often that sort of runs behind the buying new cybersecurity capabilities. Why is it that that’s so hard for people to maintain focus on over long periods of time?
Rubin: I think we just have a lot of complexity in the world and sometimes it’s not lack of desire, lack of interest, it’s certainly not a lack of realizing how important it is. We spend time with customers every day who talk to us about how basic hygiene or basic operational discipline is as important as any tool that they buy. But the reality is that we have very complex environments and even though we talk about hygiene or discipline as something very simple, we describe it as something that seems like it would be very basic, the reality is that it’s hard. Now, is that an excuse for not doing it? Is that a reason to not prioritize it? Of course not. But I do think sometimes we take it for granted that it’s not, as they say, “As easy as getting up and brushing your teeth in the morning.”
Have you seen companies that are outside of the usual suspect areas of intelligence and financial services that are good at establishing a cybersecurity awareness culture?
Rubin: I was in Australia and Asia visiting with our customers and prospects two weeks ago and I was standing in the lobby of a building and it was not a financial services firm, it was not a government agency, it was actually what we all would describe as an old-school business. It was near the elevator banks where literally all of the employees who work in this fairly large building go in and out every day and they had a series of posters on the wall and some of them were internal advertisements for programs that they were running and one of them literally was a list of basic cyber reminders. I asked the host that was taking us upstairs, “What’s the story with the poster next to the elevator?” And he said, “Actually, it’s cyber awareness month. It’s our way from the security team to talk to the organization, to sort of make sure that we take them through the basics.” And that to me, not only is it heartwarming, but it was a good datapoint to show that this is no longer just a cyber conversation for a large bank or a government agency or a business that traditionally we would have thought of as cyber paranoid or focused.
Kirner: I have three kids and they learn at school about this, we have conversations at home, we have a generational wave of people who have grown up and understand not to do these things.
A lot of CISOs, CIOs, CTOs are forced to buy cyber insurance. And they don’t like it, for good reasons, because the cyber insurance industry is very new and there are lots of escape hatches for the policies. How can CISOs turn that conversation around into something productive?
Rubin: It’s a great question. This is not a conversation that Illumio is necessarily having directly with its customers. But we are in the room with some of these stakeholders and I’ll share with you from my perspective probably the best way that I’ve heard somebody talk about it. They said, “In the unfortunate event that we were to have a breach, there are three things from an impact perspective we’re going to think about.” The one that belongs at the top of the list but is also probably the least insurable one is simply trust. In other words, I’m not sure that you can buy an insurance policy when you talk about things like will an organization, especially if it’s a consumer oriented one, lose revenue over time if they have a breach and it becomes a public event? The answer is probably yes but I’m not sure how you quantify it. Here were the two that were a lot more tangible, scopable and quantifiable: the cost of the breach. “I have to go buy a product in order to do something that I wasn’t doing before.” The actual short-term or immediate-term impact and the dollars attached to those activities. Maybe there’s an audit requirement that comes up as a result as well. But it was the second category that actually I think most people don’t think about and it was the one that stuck with me the strongest because I know I’d never thought about it which is when something happens and I have to go spend money to deal with it, fix it, change it, there’s a whole series of other things that I was planning on doing that I can’t do anymore. There’s a project that was funded that’s no longer funded because those dollars had to go somewhere else. And so in this particular CISO’s mind, the way that he actually netted it all out was very simple, “I want to make sure that I have insurance that covers the service costs of the breach and allows me to continue to run the business and make the investments I was planning on making during that fiscal period or that year. And if I could buy a policy that ensured that those two things happened then although I can’t deal with the most important one which is what are my customers going to think, I can certainly ensure that we’re able to pick ourselves up the next morning and go back to work.” And I’m not sure if that math is firm enough yet in everybody’s mind but I think it’s a fantastic framework to think about if I write a check and buy a policy, will it guarantee me those two outcomes.